As a follow up to one of my previous posts, here’s the *supported* method of querying audit events for Office 365/Microsoft 365 Group mailboxes. In a nutshell, you should use the unified audit log instead of the good old Search-MailboxAuditLog cmdlet, which for the record still only works for group mailboxes that have a primary SMTP address associated with the default tenant.onmicrosoft.com domain.
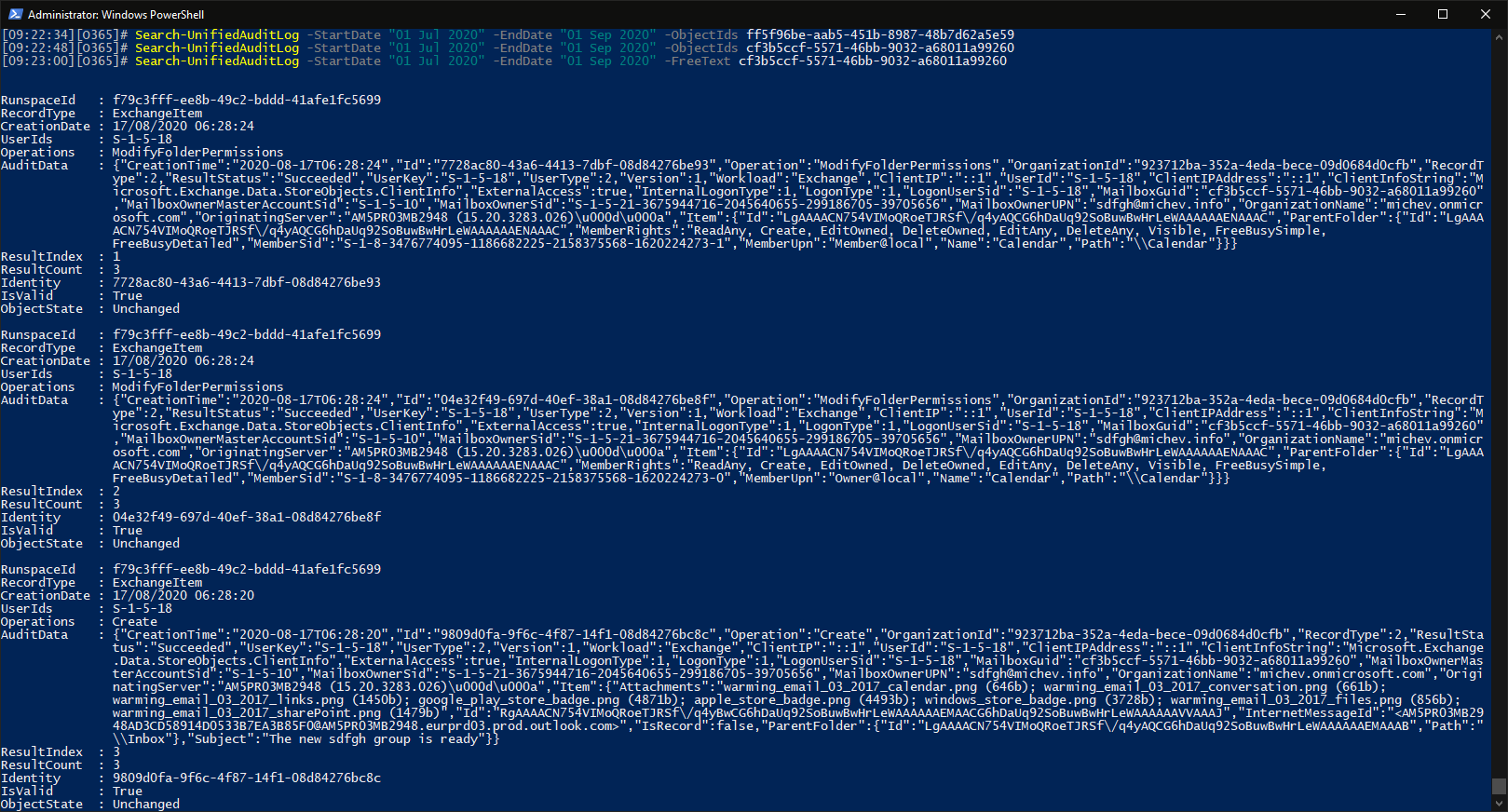
Without further ado, here’s an example that will list all the audit events for a given group for the specified time period:
Search-UnifiedAuditLog -StartDate "01 Jul 2020" -EndDate "01 Sep 2020" -FreeText cf3b5ccf-5571-46bb-9032-a68011a99260
where the GUID value specified for the –FreeText parameter corresponds to the ExchangeGUID of the group’s object. While other identifiers might also work, this is the *supported* method to query the Unified audit log for any Exchange-specific audit entries. Note that using the –ObjectIds parameter will not work here, it will always result in zero events regardless of which specific identifier you’ve provided.
You might want to further scope down the results to just mailbox audit events, by specifying ExchangeItem as the RecordType. In my experience, using the ExchangeGUID value will return just Exchange-specific events, so for the purposes of the task at hand it should suffice. Using the group’s email address will return some AzureAD events as well, while using the ExternalDirectoryObjectId will return even more AzureAD associated events. And yes, if you need a full set of events across all services, you’ll probably need to run the query multiple times.
For the sake of completeness, here’s the output of the Get-MailboxFolderStatistics cmdlet for the given group mailbox, which reveals exactly three audit entries, as returned above:
Get-MailboxFolderStatistics cf3b5ccf-5571-46bb-9032-a68011a99260 -FolderScope Recover | ft Name,Items* Name ItemsInFolder ItemsInFolderAndSubfolders ---- ------------- -------------------------- Recoverable Items 0 3 Audits 3 3 Calendar Logging 0 0 Deletions 0 0 DiscoveryHolds 0 0 MigratedMessages 0 0 Purges 0 0 SubstrateHolds 0 0 Versions 0 0
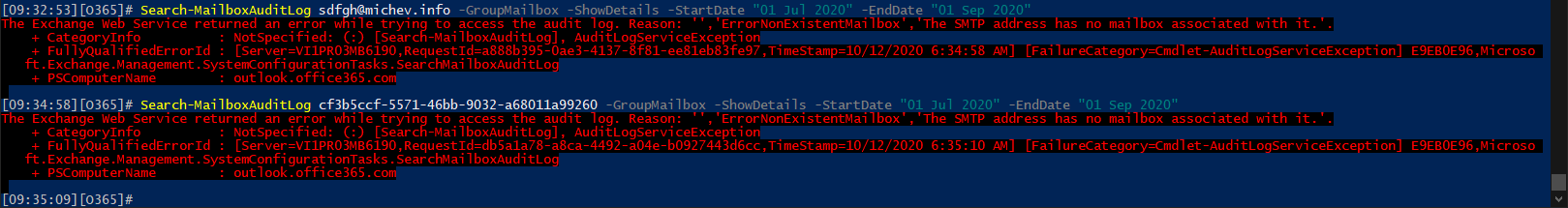
And the error you will get if you insist on using the good old Search-MailboxAuditLog cmdlet: