Continuing the Permissions inventory series, I’ve published two new scripts and their corresponding articles in the past month or so.
The first scenario deals with mailbox forwarding, as it seems to be a common ask on the different Office 365 communities/forums. There are many ways forwarding can be configured, thus the script accepts additional parameters that allow you to specify which methods to report on, or you can just run it without passing any parameters to report on “standard” forwarding. Detailed description can be found in this article or directly on the GitHub repo script page.
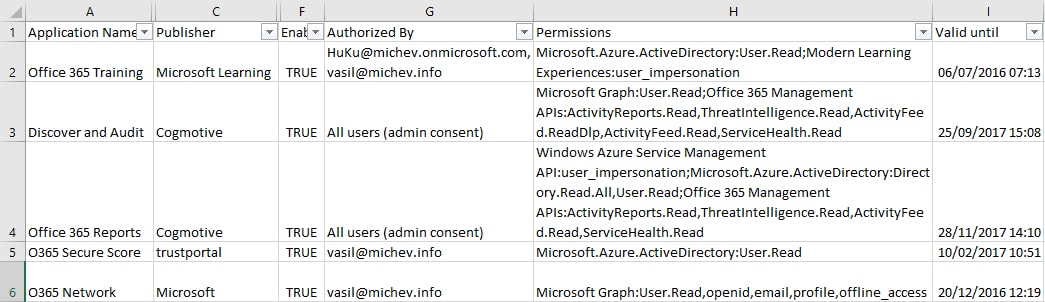
The latest scenario I’ve covered deals with reporting Azure AD integrated applications, the users that have authorized them and the permissions granted on said applications. The script only covers 3rd party apps, as I assume you are familiar with your own apps 🙂 The goal was to provide the same level of detail that can be found in the App permissions reports that are part of Advanced Security Management/Cloud App Security, without having to pay for the additional license that is. Granted, the ASM/CAS report will look way prettier than the CSV export 🙂
This time around I’ve chosen not to do the actual execution via cmdlet and encapsulate it in a script, but a more direct approach. In any case, simply running the script will return a list of all the 3rd party Azure AD applications found in the tenant, along with all the relevant information about Publisher, permissions, users and so on. If needed, you can gather some additional data as well, as I’ve deliberately skipped some attributes in order to replicate the level of detail found in ASM/CAS.
Anyway, the article describing more detail about the script can be found here, and the actual script is on my GitHub page.
As usual, let me know about any issues you run into, or any feedback in general. Or, ideas for new “inventory” scripts, as long as they cover something interesting and don’t have a dozen or so versions already available on the internet 🙂