Did you know that the recently released refresh on the Azure AD login pages features a change in behavior in validating the credentials presented? Namely, the login page will no longer inform you if you provide an invalid username, such as that does not match any existing Azure AD user.
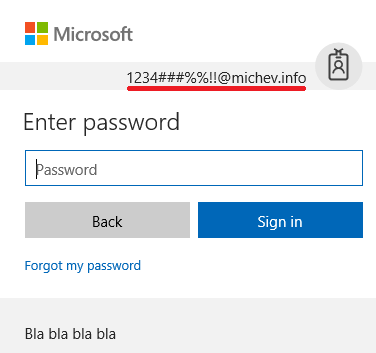
This of course does not mean that there is no error handling at all, what it means is that the page will no longer inform you that you are trying to login with non-existent account, as long as the domain portion of the UPN used matches any domain validated in Office 365/Azure AD. Even in the “extreme” cases where you enter something absolutely unacceptable for the “username” part. Here’s an example:
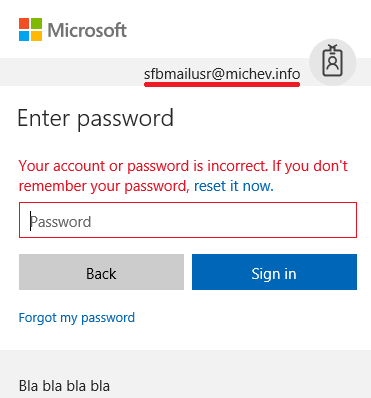
As the example above uses my personal domain, which of course is added to my Office 365 tenant, I am allowed to proceed to the “Enter password” screen, even though I’m using some absurd string for the username part. The same behavior will be observed if I simply enter any valid username string, which does not correspond to a user account present in my Office 365 tenant. For example, if I make a small typo and misspell the credentials for one of my test accounts, SfBMailUser@michev.info:
The error will be displayed only after you have entered the password, and it is generic enough as to not give you any clues whether the username was the wrong part. Overall, I’m happy with the change, as while it might be a slight inconvenience when I occasionally try to login with the incorrect username, the benefit is having more secure login process. Previously, one was able to just bulk test various username combinations and the login page would happily let you know if any of those corresponded to actual usernames present in the service.
I’m not sure if this change was introduced with the switch to the new login pages, so I cannot tell how long it has been available (or how I’ve missed it), but it surely is a welcome change, as it makes brute force attempts less likely to succeed. I for one have always wondered why Microsoft decided to incorporate such error handling in the first place, so I can sleep in peace now 🙂