Over the past few years Microsoft has been releasing more and more cloud-enabled features and integrations for Windows 10. Activity history is one such feature, designed to synchronize information about apps and services you use, browsing data, media files played and more, across all your devices. Activity history in turn powers the Timeline, which you can find under the Task View button, or by pressing Win+Tab. With the 1809 release of Windows 10, we also got the Cloud Clipboard, another example of cloud-reliant feature, which syncs your clipboard history across devices.
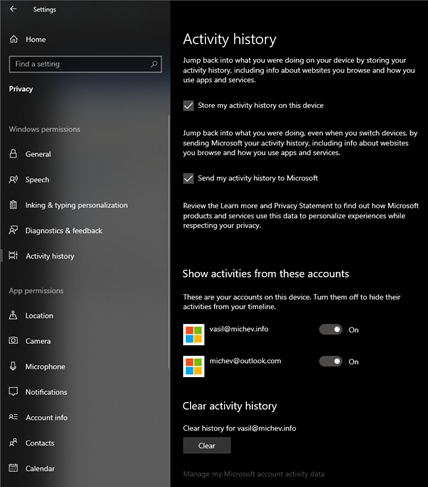
Such features are often turned on by default, so inevitably some sensitive data ends up stored in the cloud, which in turn raises privacy concerns. Even though Microsoft introduced controls to disable gathering of activity information, users have reported cases of such information still being gathered with all the controls toggled off.
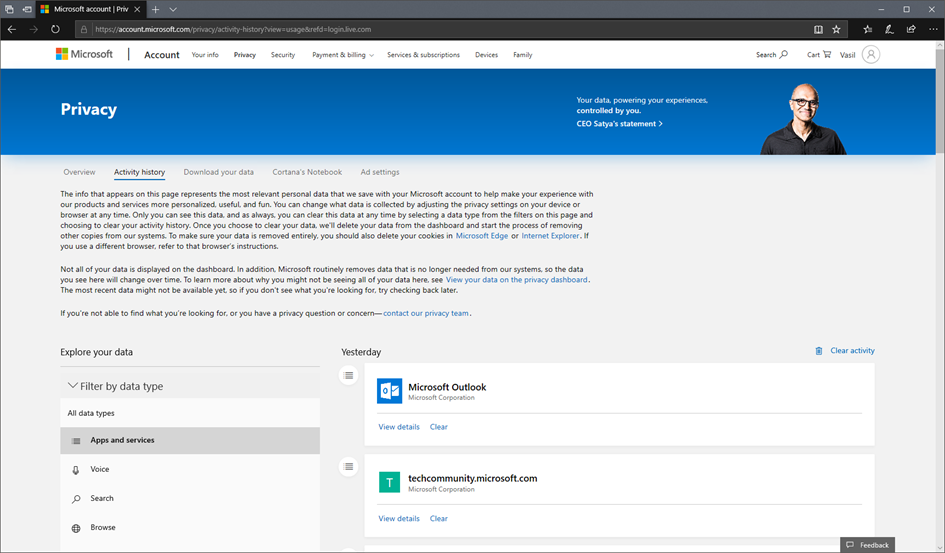
The question on how and where exactly this data is being stored is an interesting one to explore. To get an overview of the various type of activity information Microsoft is storing, you can use the Activity history page of the Privacy portal: https://account.microsoft.com/privacy/activity-history. The dashboard is depicted below:
An important note is due here – the Privacy portal can only be accessed via a MicrosoftID. In effect, if you have a device that’s Azure AD joined and only the organization account is configured, the dashboard will not be accessible. Yet, even in such cases the activity information is being displayed on your timeline. So where is the data stored then? The answer is – in your Office 365 mailbox. You might not see any indications of that, as it’s all hidden under the covers of the non-IPM subtree.
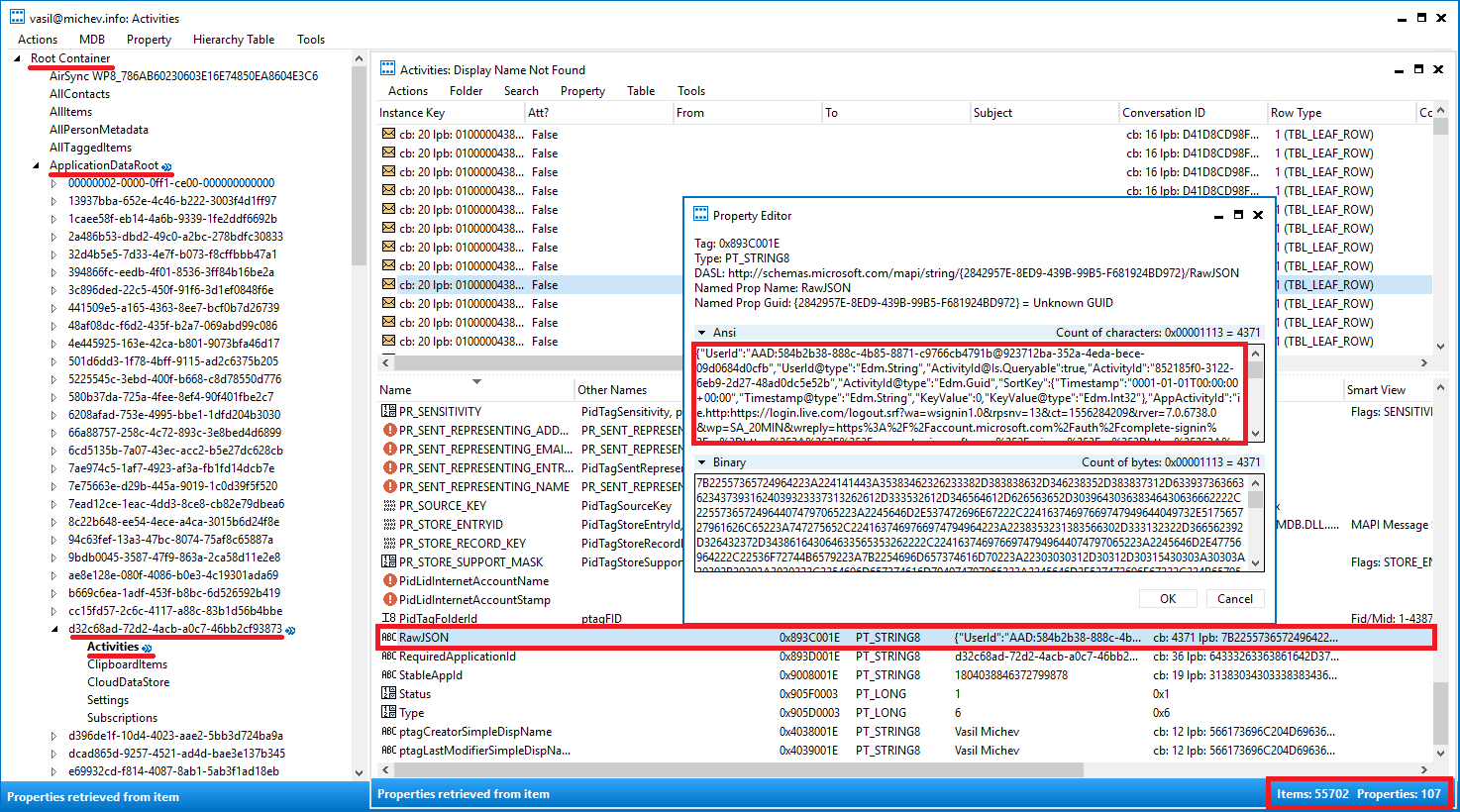
To access and work with the activity data stored within your mailbox, you can use some low-level utilities such as MFCMAPI. It’s beyond the scope of this article to cover the basics of using MFCMAPI, so if you need additional instructions check out the gallery of articles available here.
After you’ve opened the message store with MFCMAPI, expand the Root Container node and select the ApplicationDataRoot entry. This folder is the “standard” placeholder for any application to store their own data in, within the confines of the user’s mailbox store. Storing data inside the Non-IPM subtree isn’t something new and various applications have been doing it for years, often without following any guidelines or schemas, as evident from the numerous other top-level folders you can find within the store.
If you expand the ApplicationDataRoot node, you will see a list of various GUIDs, each corresponding to a given application. For example, the 501d6dd3-1f78-4bff-9115-ad2c6375b205 entry corresponds to the Events from email feature, b669c6ea-1adf-453f-b8bc-6d526592b419 is where Focused Inbox does some of its magic, MyAnalytics uses 3c896ded-22c5-450f-91f6-3d1ef0848f6e and so on.
In our case, data related to user’s activities is being stored in the d32c68ad-72d2-4acb-a0c7-46bb2cf93873 container, more specifically under the Activities subfolder. As you can see from the screenshot below, over 55k items are currently stored in said folder in my mailbox, detailing my activities over the past year or so. Each of those items corresponds to a single activity, with the activity details stored in a JSON format inside the RawJSON property:
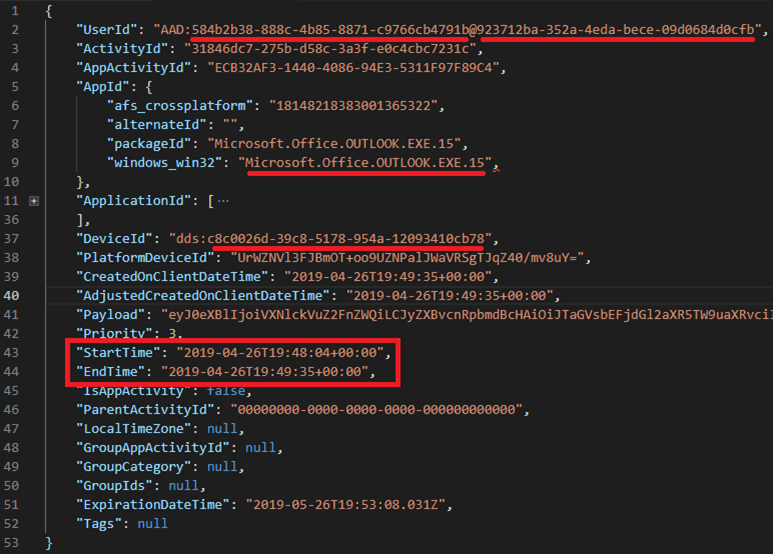
The JSON string itself stores information about the user performing the action, the device and platform, the application used and resources accessed, timestamp and more. In the example above, an URL is visible, indicating that the activity in question was captured from one of my browsing sessions. As another example, here’s an activity captured for an action performed in Outlook, with the JSON expanded and trimmed to show only the more interesting properties:
From top to bottom, we have the ObjectId of the user performing the action, followed by the TenantId. Application information is gathered next, as well as the DeviceId, start and end timestamps, and so on. By fetching all the individual messages corresponding to events for a given date, or for the past 30 days, one can reconstruct the timeline presented by Windows in the Task View.
Apart from activities information, another interesting type of data stored under the d32c68ad-72d2-4acb-a0c7-46bb2cf93873 container is the content of your Cloud clipboard. Indeed, if you browse the ClipboardItems subfolder, you will see items with similar set of properties to the ones detailed above. As before, the RawJSON property contains the interesting bits of information, with the actual copied item being stored in encoded form in the Payload property. Here’s a snapshot of one of the ClipboardItems stored in my mailbox:
To get to the actual copied content, we can use PowerShell to invoke the corresponding .NET methods in order to convert the Base64-encoded string to a human-readable one. This in turn will output another JSON string, decoding the content property of which will give us the final result:
As it turns out, the example item represents some text I’ve copied out of the sponsor chapter of the Office 365 for IT Pros book, probably while making changes to it last month.
Of course, clipboard items are not always just plain text content, so using the method outlined above might not generate acceptable results every time. The general idea still applies though – you enumerate each item in the ClipboardItems subfolder, get the RawJSON property and decode the Payload value to get the content of the clipboard item created at the given time and date.
So, now that you are aware that the Activity history and Cloud Clipboard data is being stored inside your mailbox, does this make you feel safer or?


I think in some cases it should be stored locally. Say on my last job we were using Office 365, but devices were not Azure AD joined or hybrid joined, so Timeline was warning it will save only a week or so of data. I guess then it is saved somewhere on disk (maybe registry).
Yup, you are right, there’s a local store as well. I was only covering the “cloud” part.